The Hunter is Being Hunted: The Dogfight Among Sandwich Attackers
No one is immune to attack in the dark forest of DeFi.

Key Takeaways
No one is immune to attack in DeFi. NO ONE.
A Sandwich arbitrage attacker who is attacking can be the target of another attacker's squeeze.
The gas fees and miner tips are the reasons for these embedded Sandwiches.
It's critical to keep the balance between profit and arbitrage costs generated by gas fees and miner tips.
On Ethereum, not all arbitrages are created equal. For example, Spatial, Triangular, and Combination arbitrages increase the efficiency of the crypto market. On the other hand, front-running arbitrages, like High-Frequency Trading on Wall Street, take advantage of the everyday traders to benefit the attackers, also known as searchers. According to CoinMarketCap, the searchers have extracted almost $608 million on Ethereum alone.
However, the searchers can also be the target of other searchers, in other words, being sandwiched.
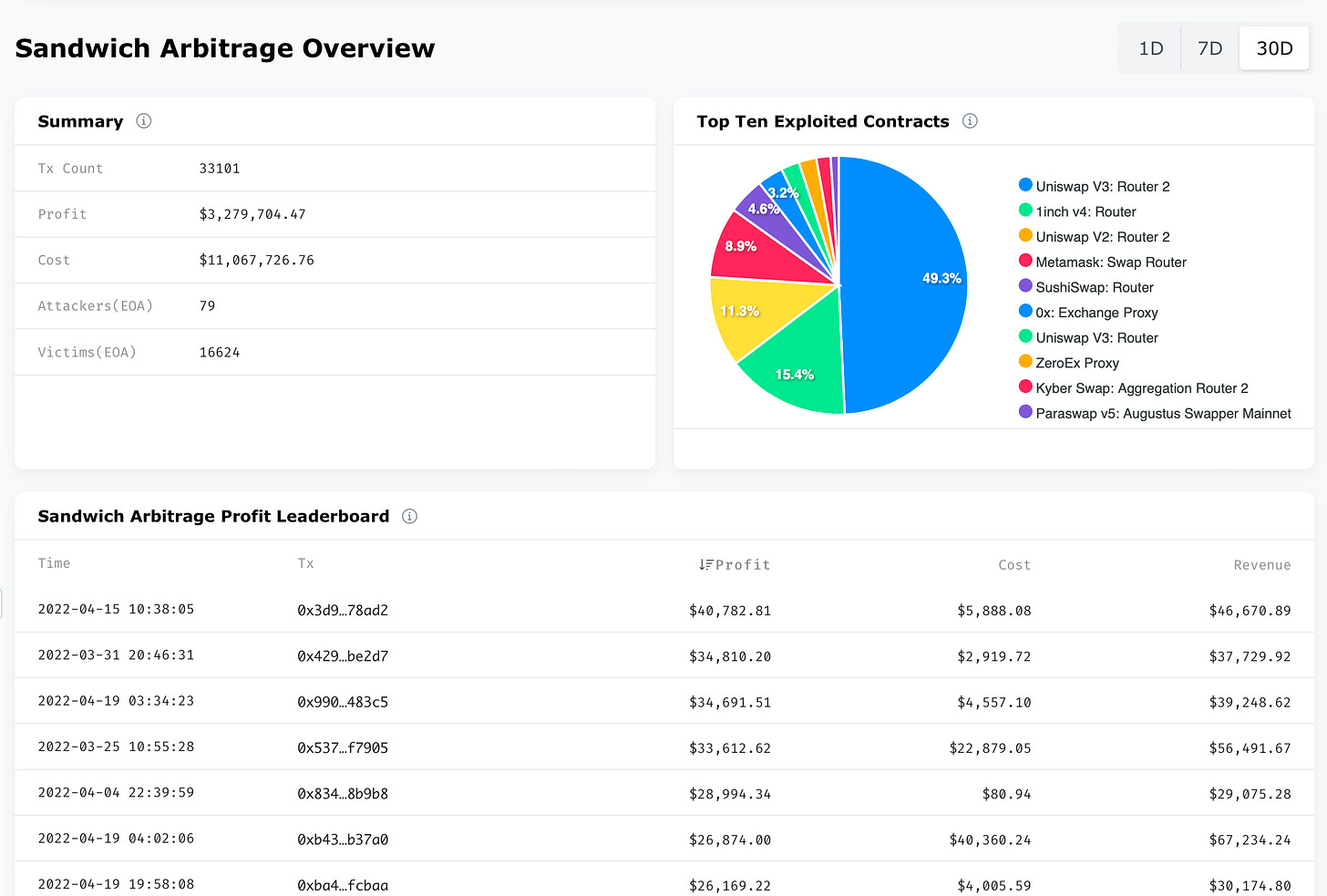
As the only exclusive DeFi MEV arbitrage Big Data platform, EigenPhi has been actively monitoring and sharing insights on the said transactions via our Sandwich Arbitrages module. Here you can find the transactions summary of specific time windows, the top 10 exploited contracts, LPs, and protocols, the leaderboard of the profit arbitrages, the attacker leaderboard, and the victim leaderboard.
This time, we'd like to tell you a story comprised of two Sandwich arbitrages and five transactions involving three participants, including two attackers and two victims, one of which is also an attacker of the two. And the plot of this story has been happening once or twice every day on Ethereum.
Let's lift the curtain.
Breaking Down the Sandwiches
Here are the two Sandwich arbitrages on https://eigenphi.io/.
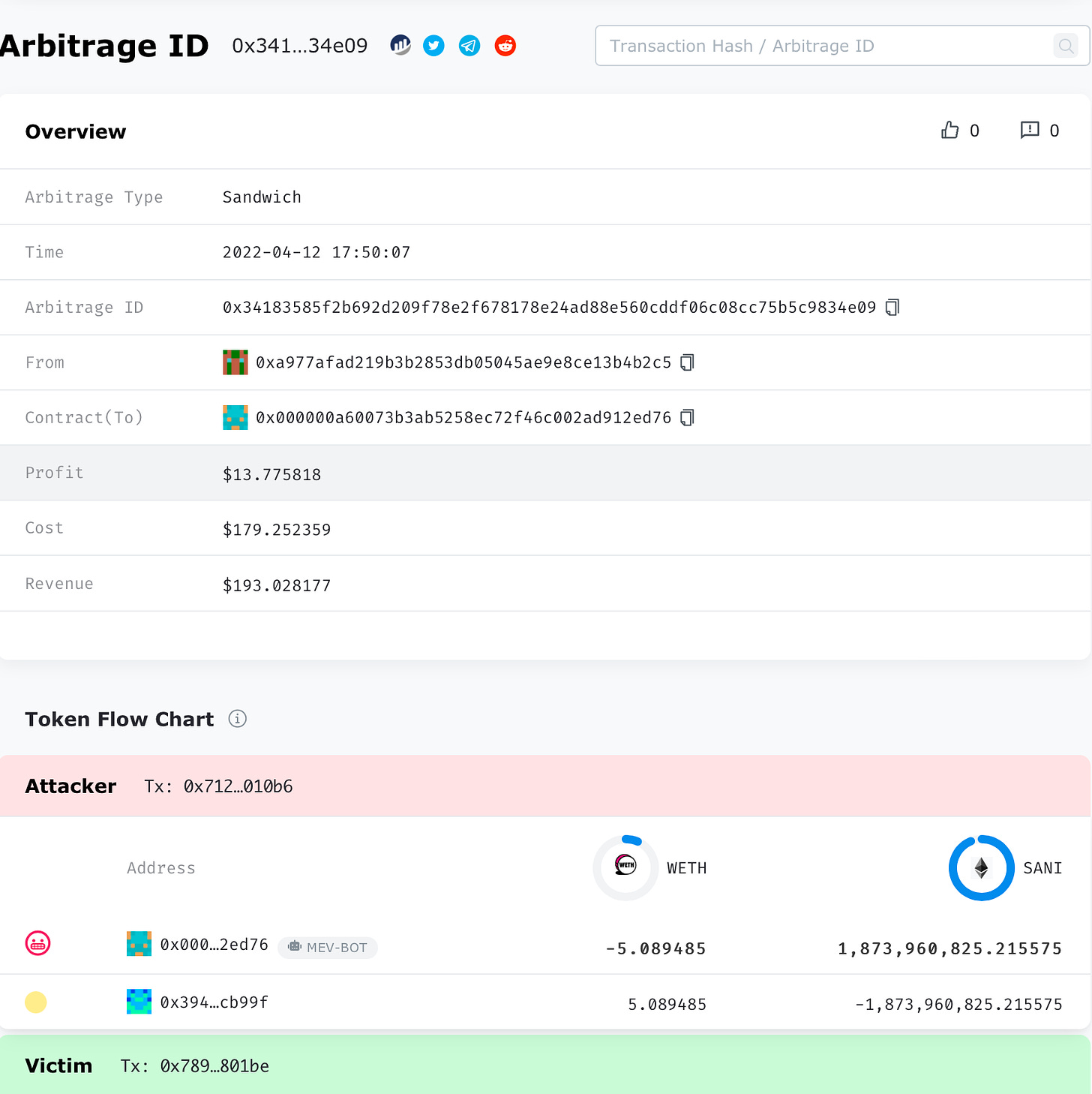
The Victim Sandwich Arbitrage. For the sake of clarity, we will call it VSA later.
The Attacker Sandwich Arbitrage. We will call it ASA later.
The two victims whose links you can click to view their victim role profile are:
Victim 1 wanted to exchange $SANI for $WETH.
Victim 2 is also an attacker, whose attacker role profile is here, attacked Victim 1.
The two attackers whose links you can click to view their attacker role profile are:
Attacker 1 is the Victim 2 above.
Attacker 2 is the one who sandwiched Attacker 1 in the ASA.
The description below will omit some of the token trading details to paint a clearer picture of the whole show. You can read our Sandwich detail introduction and the dissection of a $APE-related Sandwich arbitrage.
The table here displays how the attacks happened in chronological order.
It all started with Victim 1's intention to exchange $SANI for $WETH.
In ASA, Attacker 1 detected Victim 1's plan in the mempool of block 14573295 and deployed a transaction first to exploit Victim 1. We marked this one as Tx0 and Victim 1's transaction Tx1.
In a Sandwich arbitrage, Attacker uses two transactions to squeeze the victim. Therefore, Attacker 1 dispatched another transaction, Tx3, to finish the squeezing.
But Attacker 1 didn't know that Attacker 2 had seen Tx3 in the mempool of block 14573295 and deployed Tx2 first to squeeze Tx3. After Tx3, Attacker 2 deployed Tx4, finishing the arbitrages.
By calculating based on the price of $WETH when the transactions happened, Attacker 2 harvested $13.775818 as revenue, $179.252359 gas fee cost deducted. Speaking of Attacker 1, the poor guy lost $36.865717 gas fee cost and $79.082086 worth of $WETH.
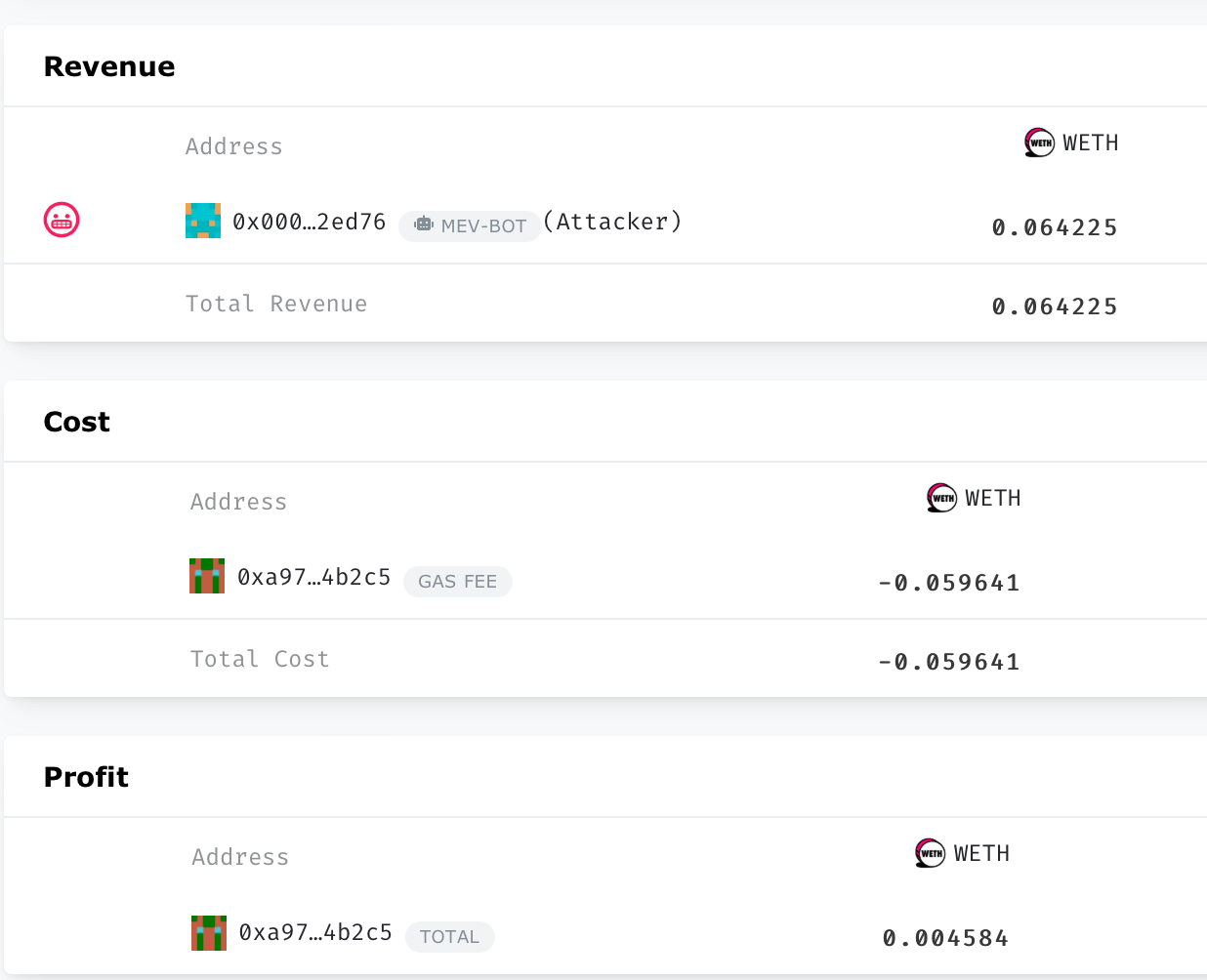
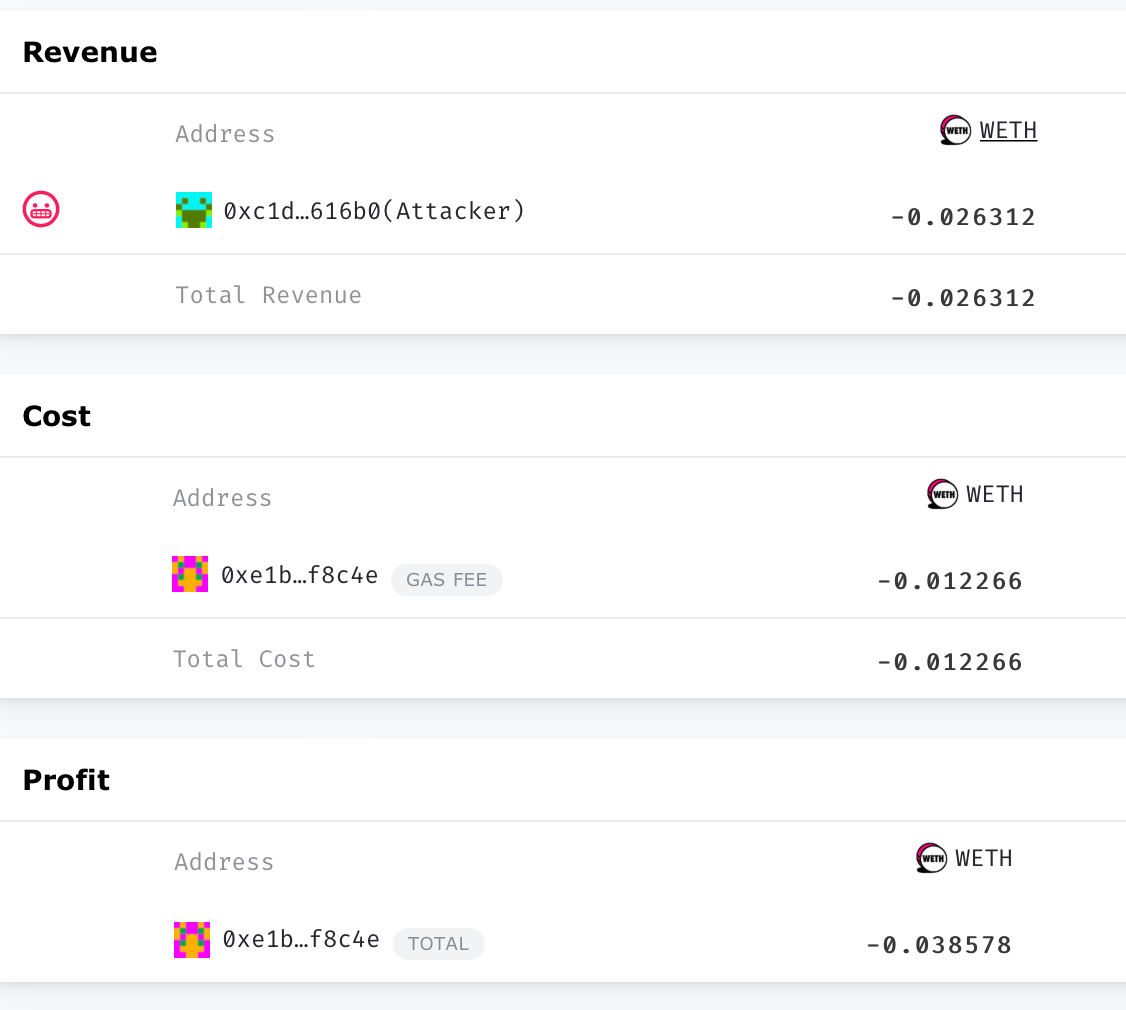
Why could a Sandwich Attacker become a victim of a Sandwich arbitrage? It seems like the result of less gas fee/miner tips, 0.012266 $WETH, provided by the Attacker 1, compared to the higher gas fee/miner tips, 0.059641 $WETH, supplied by the Attacker 2.
But that's not the whole story.
Lost the Battle But Won the War?
A higher gas fee strategy could be helpful to squeeze another Sandwich attacker once. But in the long run, it could bring less profit.
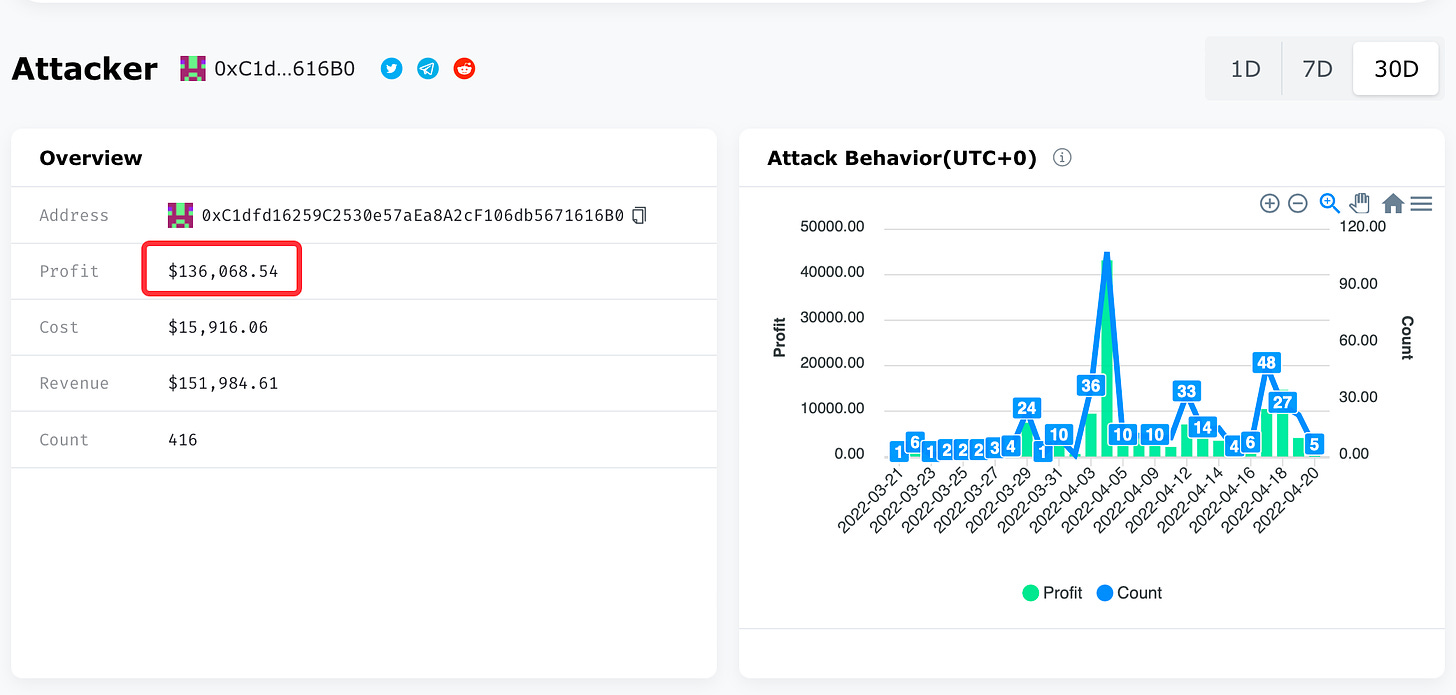
Open Attacker 1's attacker profile on https://eigenphi.io/ and choose the 30D as the time window; you can see the profit of this period is over $136K. And the cost is $15,916.06 on 416 arbitrages.
On the other hand, check out Attacker 2's attack profile:
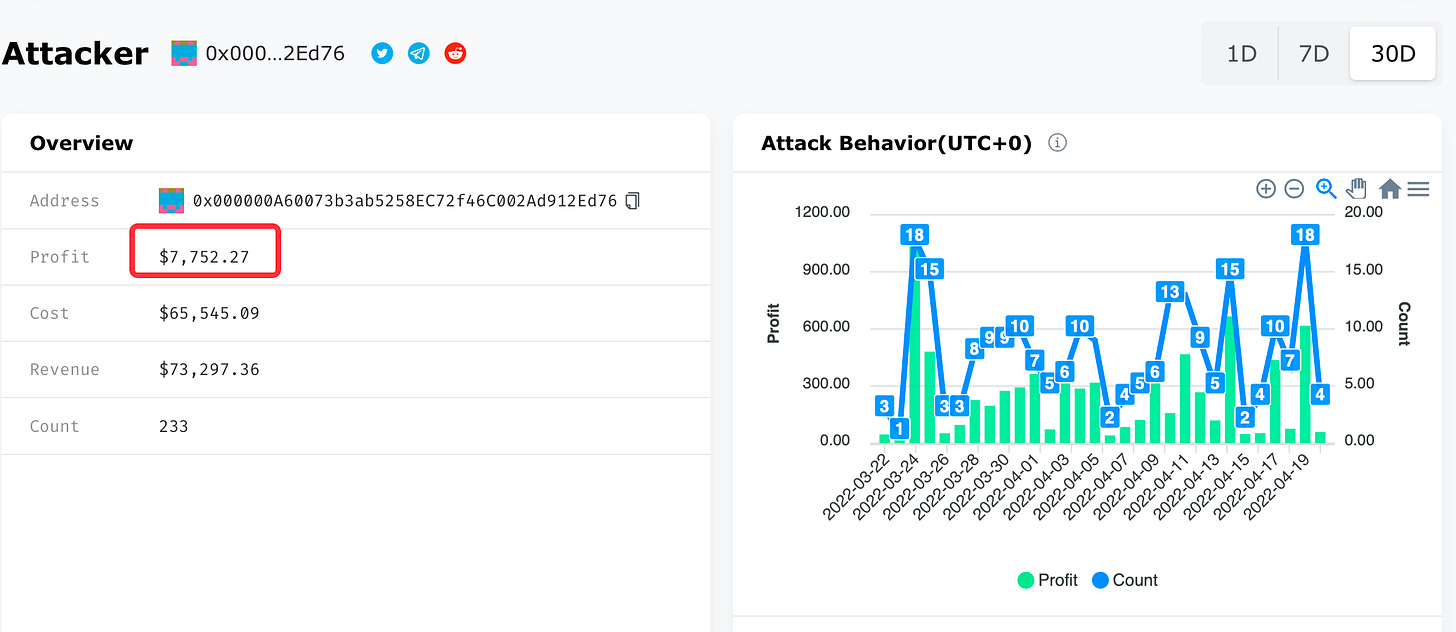
Over the last 30 days, Attacker 2's cost has reached over $65K on 233 arbitrages, thus dragging down the profit to $7.752.27. So this guy has not been as profitable as its victim!
However, in the same time period, there is no victim history recorded on https://eigenphi.io/ regarding Attacker 2.
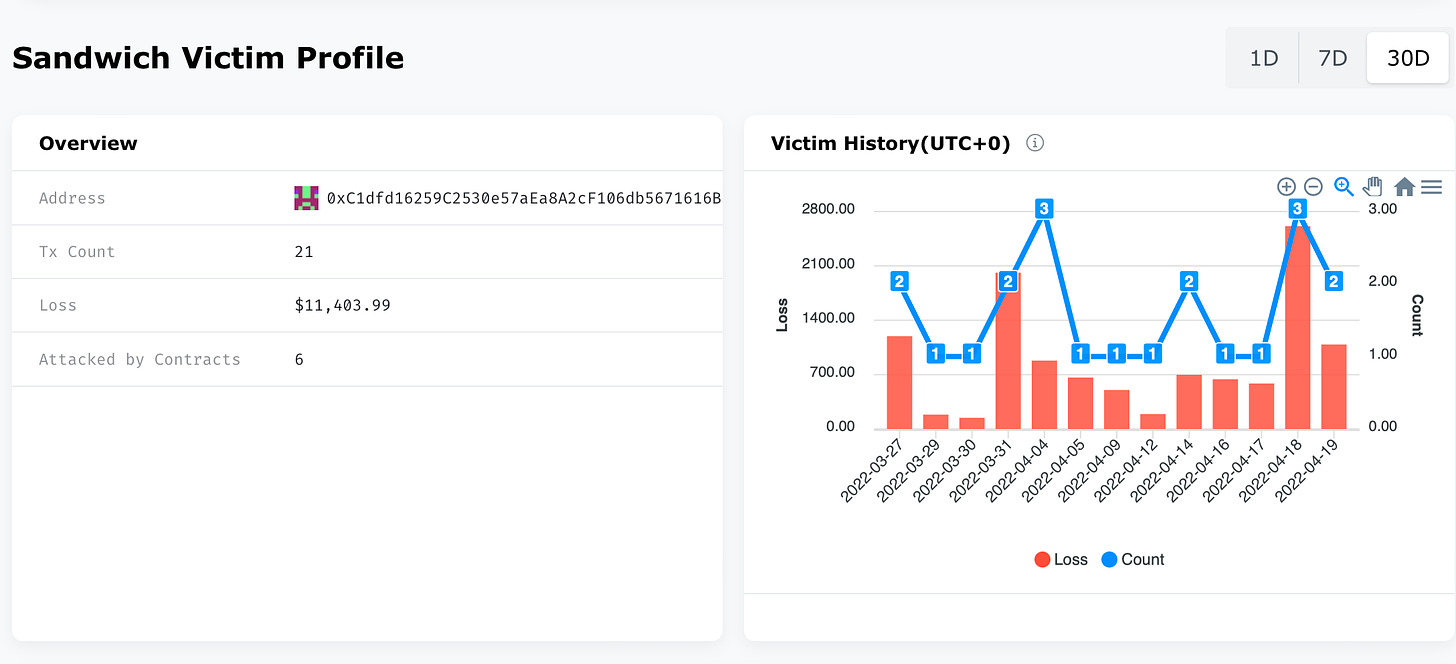
How about Attacker 1's victim history?
It turned out Attacker 1 lost $11K over 21 Sandwich arbitrage attacks. Even though, Attacker 1 still did better at the pincer war except for losing the embedded Sandwich battle.
So, who is going to have the last laugh? But unfortunately, the dust has not settled down yet.
Nobody is Invulnerable in the Dark Forest
In conclusion, in the dark forest of DeFi, everyone could be a target, no matter who you are, even a Sandwich attacker. To avoid being attacked, sending more miner bribery might be helpful. And don't forget to use flashbots' bundle. That being said, it's important, maybe almost impossible, to find the fine line between being attacked and maximizing profit.
If you are intrigued to find out more about dogfights, check out our Sandwich arbitrage Module at https://eigenphi.io/. You can tell us your discovery by sending an email to contact@eigenphi.com or just tweeting us.
Have fun hunting! (Not being hunted!)
Follow us via these to dig more hidden wisdom of DeFi: